Spyware
Spyware is something that has been becoming increasingly common on systems. It has become a more common problem than virus infections. Spyware infests your system, compromises privacy and security, and goes on to bog down system performance and Internet bandwidth. These malicious programs get lodged in your system and run in the background taking up valuable system resources and can render the speediest 3.2GHz system helpless, making it act like an old 266MHz machine on a good day.
The first thing to do on a system before any actual performance tweaks is to run spyware scans. Scanning with both Lavasoft’s Adaware and Spybot Search and Destroy. What one doesn’t catch, the other does. Using both programs can make the system squeaky clean once again. If you run across any problems in trying to remove certain pieces of spyware, try running both programs from within safe mode.
So, what exactly is it? “Spyware” is a fairly loose term to describe any software installed on your system that sends information from your computer to another destination on the Internet without your knowledge or explicit consent. Information sent could be data collected on browsing habits, such as URLs, IP addresses and cookies. Any data on the hard drive also could be sent. Key loggers and system recorders can also go as far as to record anything you type or do on your computer, thus collecting keystrokes, passwords, and other possibly sensitive information. Spyware seriously compromises system security and your privacy. Most of the time, spyware is installed using tricky methods to gain your consent. It is sometimes bundled with other software packages, such as KaZaa Media Desktop or the first version of RealOne Player (following versions have been cleaned up somewhat). Other sly methods include clicking on ads, or agreeing to install some obscure plug-in when visiting web sites. Basically, spyware is software that is not helpful to you, the user, in any way. Adware, browser hijackers, malware, and scumware/thiefware all loosely fit under the spyware category, however there is a difference between all of these and ad-supported software.
Ad-supported software merely displays ads to help pay for the freeware/shareware product. Opera and Eudora are two examples of ad-supported software. Ad-supported software crosses the line when it starts to collect data on user habits, which may or may not help the company, but it surely does not help you in the moments it is using system resources to send information. Browser hijackers are the next level in spyware annoyances, for they take over your browser and display advertisements often not suitable for all ages. Malware is anything that acts destructively toward your system, such as a trojan, worm or virus. Scumware/theifware is more or less actual theft where sneaky pieces of software try to underhandedly divert advertising revenue from other websites to themselves, usually with “contextual advertising”. This however, is not as common as the other forms of spyware.
Is spam spyware? No, however it is still a problem and a big annoyance. Spam mainly sends advertisements, but can also be carriers for spyware and malware if it happens to have an attachment and/or is an HTML message. All this sounds scary, no? Now for the million-dollar question, do you have to meekly submit and accept all of this junk? No. The spyware removal tools mentioned earlier do an excellent job. Software firewalls, such as Kerio Personal Firewall and Sygate Personal Firewall help to block spyware traffic from entering/exiting your system. Last but not least, good AntiVirus software, such as Grisoft’s AVG. Upon the completion of these scans, you may want to make a clean registry backup and system restore point. Now that a large portion and the most common problem of performance hogging has been taken care of, on to some of the Windows tweaks themselves!
Tweaking Software
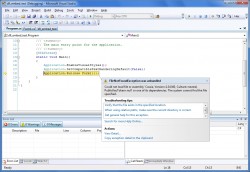
Microsoft recently released a small tweaking package for Windows 2000, 2003 Server, and XP called “Tweak UI”. Basically, it allows the user to configure various interface settings without having to spend time digging through the registry. It can be downloaded here for XP, and here for 2000. There are a few tweaks included in this article that can now be adjusted via this tweak tool, so in addition to instructions for the tweak using the registry, instructions on how the tweak can be applied using the Tweak UI tool will also be noted.
Some of the more complex tweaks that do not involve the UI (User Interface) have downloadable *.reg files included with the instructions so that you can apply the tweaks directly to your registry without having to actually delve into fray and make the necessary adjustments by hand. All you have to do is download them, run them, and click “Yes” when prompted.



 AdamTheTech.com and respective content is Copyright 2003-2025.
AdamTheTech.com and respective content is Copyright 2003-2025.